A Closer Look at the Chain of Trust Security Architecture: Provisioning and Secure Boot
Published on April 10, 2019
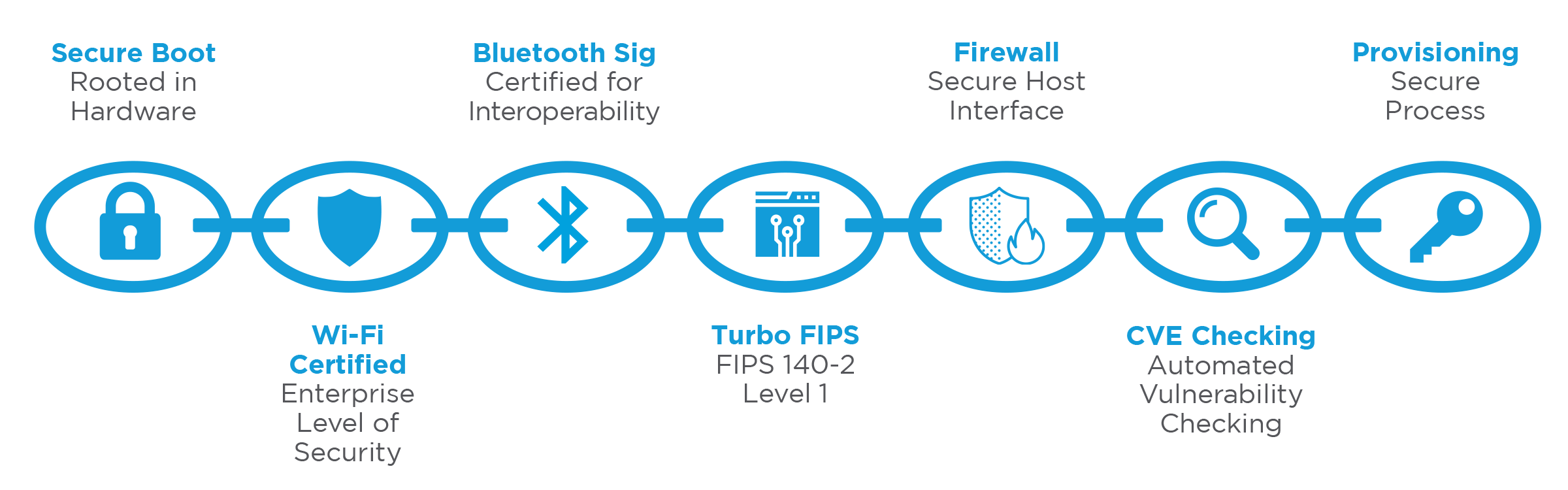
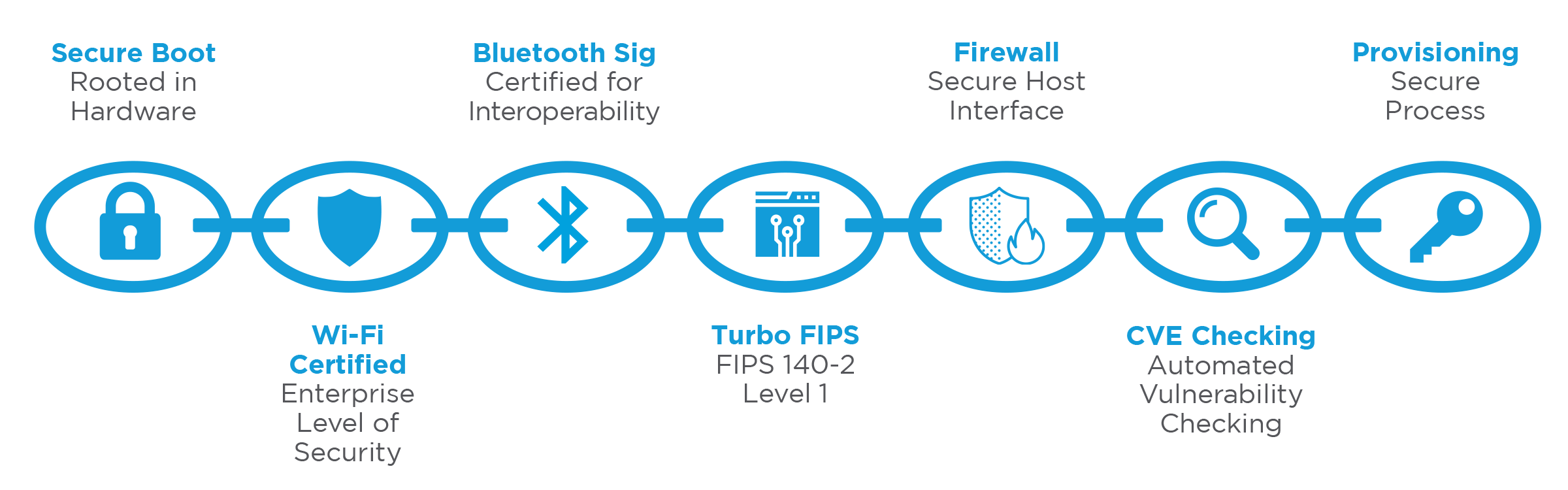
In medical and industrial applications, security is a critical component to wireless designs. It is also an increasingly complex goal that requires more comprehensive approaches to ensure networks and devices are protected. Ezurio's (formerly Laird Connectivity) Chain of Trust architecture secures software images running on our 60 Series system-on-module (SOM) and Sentrius™ IG60 gateway. This architecture mitigates risks from attackers looking to exploit common vulnerabilities on these platforms. This blog series will take a closer look at each link of the Chain of Trust. To start, this post will cover Secure Boot and Provisioning.

SECURE BOOT
The Secure Boot process, currently in development, starts with the Hardware Root of Trust. Laird maintains a secure production environment and manages the secure provisioning of keys during the production process. Each module and gateway are configured with unique Hardware Root of Trust keys. The keys are randomly and cryptographically generated using industry-standard algorithms, making them nearly impossible to guess with brute force attacks.
The secure keys are used to sign software images and support Secure Boot for each device. The Secure Boot process will enable the Hardware Root of Trust to be chained to all executable code for the Laird products enabling verification of every bit of code running on the module. The device will not boot unless the code and data loaded from the flash memory matches the unique predetermined hash generated during production. Secure Boot also controls the available boot sources. As an example, insecure boot paths such as serial or USB ports are disabled permanently during the production process.
One example of an attack that could have been mitigated by this approach is Stuxnet. The Stuxnet worm attacked industrial control systems by loading illegitimate firmware over a USB key that modified the expected behavior of the control system while silencing alarms that indicated there were problems. Because these virulent firmware images were not validated by a secure boot process, the boot process identified the files on the USB key as a firmware update and took the changes.
SECURE PROVISIONING
The Chain of Trust security architecture provides a mechanism to provision and update software with signed images, preventing unauthorized or rogue software from loading into the device. The Chain of Trust architecture verifies at every layer the software running on the Laird device. The Chain begins with the boot code that is encrypted with the same key during provisioning, thus ensuring the contents remain secret and can be verified as trustworthy. This proprietary and secure implementation protects against modifications to the 60-SOM and IG60, preventing the loading of insecure images or the enabling of external boot processes.


The Ezurio Chain of Trust architecture includes an encrypted file system to store confidential information such as network credentials, passwords, or other configuration details deemed sensitive by the end user or areas like hospitals where the unit is deployed. This protects any stored credentials or configuration details from exposure to hackers and intruders. Designing and building secure products is only the beginning; software and image updates are required over the life of the product to improve performance, add features, and fix security vulnerabilities. Over time, unpatched connected devices become one of the largest potential attack surfaces, given that their security vulnerabilities become well-known and easily exploited. The reason is simple – an attacker can scan a network to find devices with old firmware, then simply take advantage of well-known, well-documented vulnerabilities without having to first do the hard work of discovering how to attack the device. This type of attack is so simple that it can be fully automated and deployed by amateur hackers.
By working in partnership with our customers, it is possible to ensure all devices are up to date. This may include Ezurio managing the update process to connected devices in the field over the air, as well as making updates available to our customers and end users where a physical update of the device may be required. This will be covered in a subsequent blog post from Laird, coming soon.
 Laird Connectivity is now Ezurio
Laird Connectivity is now Ezurio